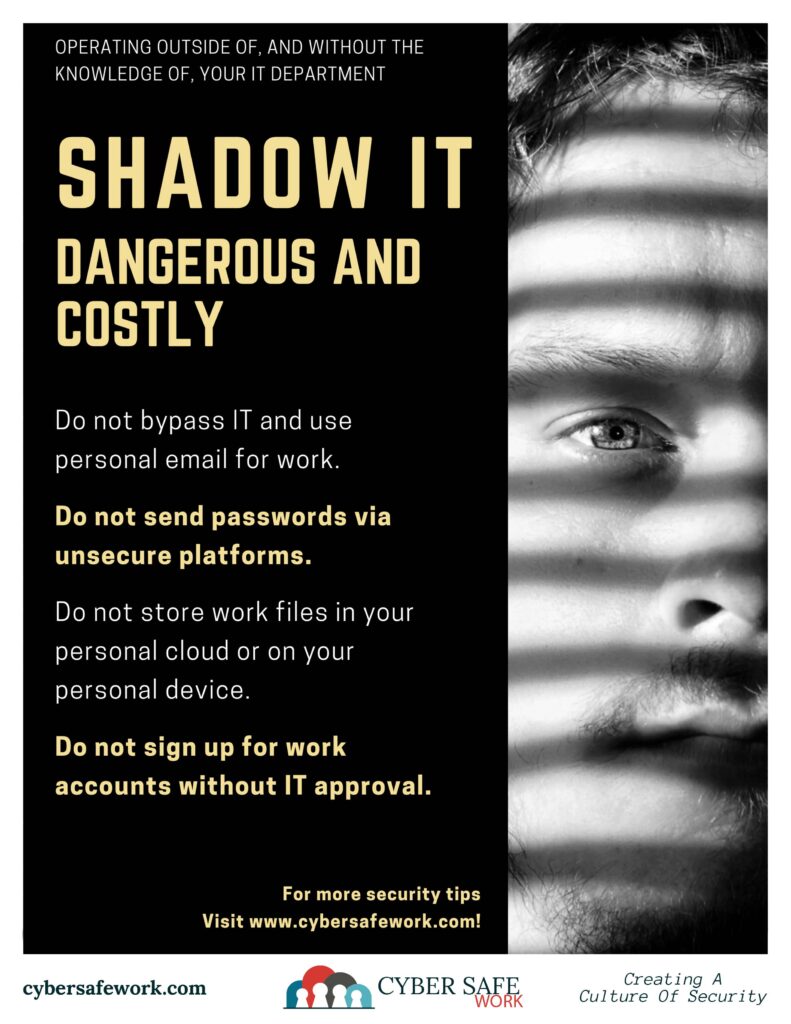
Shadow IT is defined as any IT services, not set up or documented by an oversight authority, usually an IT department. Every undocumented, and unmonitored, IT service creates a weak link in security which can result in a breach.
Sometimes it seems easier to send the email, share a password, copy documents to the cloud or sign up for services without getting approval from the IT department. However, this ungoverned or unmonitored approach to everyday business tasks can be dangerous and costly. Here are four ways the Shadow IT can cost your organization money.
I didn’t know my email was hacked.
It is important to use monitored email for reasons that go beyond a simple hack. The IT department within your organization is probably monitoring what goes in and comes out of the organization. Therefore, if there is ever an issue with an email hack, the IT department can shut it down. When using personal email addresses, the IT department has little to no chance to intervene on your behalf if there is an issue. It is also worth noting that some organizations are bound by government regulations regarding record keeping. The IT department may have an email archiving system in place for this reason. Whereas your personal email address probably doesn’t archive old emails.
Sure, I’ve sent passwords through email.
Because email is so prevalent and easy, people often fire off email without much thought. It is important to remember that most email is not secure. Neither are most instant messaging programs, spreadsheets, and certainly not sticky notes. Sharing passwords is not a great idea to begin with. But sharing passwords using an insecure method can mean hackers can intercept the message and gain access to sensitive programs or information costing your company or organization.
I store work files in my personal cloud storage.
Before sending work files to your personal cloud storage solution, check with the IT department on their policies. Work files do not belong on personal storage devices. If you need to work from home, use company-approved methods. Cloud storage and mobile devices secured by weak passwords can make it easy for company data to leak into the wrong hands. Further, if your personal cloud service is compromised without your knowledge, that can put your company at risk.
I’ve created accounts for work without notifying IT.
It may seem easier to sign up for accounts without going through IT, especially if it makes your job easier. However, if IT does not know the software used in the office, IT cannot mitigate problems. Something as simple as a software update may keep your information secure. Your IT department can only keep track of the software they know about.
Visit www.cybersafework.com for more security tips!
